https://bit.ly/2vMQaea
25 Apr 2018
13 Apr 2018
11 Apr 2018
How to Build a Low-Cost, Extended-Range RFID Skimmer
Abstract:
Radio-Frequency Identifier (RFID) technology, using the ISO-14443
standard, is becoming increasingly popular, with applications like
credit-cards, national-ID cards, E-passports, and physical access
control. The security of such applications is clearly critical. A
key feature of RFID-based systems is their very short range: Typical
systems are designed to operate at a range of 5-10cm. Despite this
very short nominal range, Kfir and Wool predicted that a rogue
device can communicate with an ISO-14443 RFID tag from a distance of
40-50cm, based on modeling and simulations. Moreover, they claimed
that such a device can be made portable, with low power
requirements, and can be built very cheaply. Such a device can be
used as a stand-alone RFID skimmer, to surreptitiously read the
contents of simple RFID tags. The same device can be as the
``leech'' part of a relay-attack system, by which an attacker can
make purchases using a victim's RFID-enhanced credit card--despite
any cryptographic protocols that may be used.
In this study we show that the modeling predictions are quite
accurate. We show how to build a portable, extended-range RFID
skimmer, using only electronics hobbyist supplies and tools. Our
skimmer is able to read ISO-14443 tags from a distance of
 25cm, uses a lightweight 40cm-diameter copper-tube
antenna, is powered by a 12V battery--and requires a
budget of
25cm, uses a lightweight 40cm-diameter copper-tube
antenna, is powered by a 12V battery--and requires a
budget of  $100. We believe that, with some more effort, we can
reach ranges of
$100. We believe that, with some more effort, we can
reach ranges of  35cm, using the same skills, tools, and
budget.
35cm, using the same skills, tools, and
budget.
We conclude that (a) ISO-14443 RFID tags can be skimmed from a distance that does not require the attacker to touch the victim; (b) Simple RFID tags, that respond to any reader, are immediately vulnerable to skimming; and (c) We are about half-way toward a full-blown implementation of a relay-attack.
We conclude that (a) ISO-14443 RFID tags can be skimmed from a distance that does not require the attacker to touch the victim; (b) Simple RFID tags, that respond to any reader, are immediately vulnerable to skimming; and (c) We are about half-way toward a full-blown implementation of a relay-attack.
1 Introduction
1.1 Background
Radio Frequency Identification (RFID) technology, using the ISO-14443 standard [ISO00], is rapidly becoming widely adopted by many governmental, industrial and commercial bodies. Typical applications include contactless credit-cards, national-ID cards, E-passports, and physical access control (cf. [Fin03], [GSA04]). The security of such applications is clearly critical.A key security feature of RFID-based systems is their very short range: ISO-14443 systems are designed to operate at a range of 5-10cm. Thus, the perception is that the RFID tag (or smartcard) must almost touch the RFID reader, which should imply that the tag's owner is physically present and holding the tag. Unfortunately, this perception is incorrect. Recently, Kfir and Wool [KW05] described a relay-attack on RFID systems, that violates the implication that the tag being read is in fact near the RFID reader. Their system architecture involves two devices, a ``leech'' and a ``ghost'', that communicate with each other (see Figure 1). Such a system would, for instance, allow an attacker to make purchases using a victim's RFID-enhanced credit card--despite any cryptographic protocols that may be used.
As part of their work, [KW05] predicted that the rogue ``leech'' device can communicate with an ISO-14443 RFID tag from a distance of 40-50cm, based on modeling and simulations. Moreover, they claimed that such a device can be made portable, with low power requirements, and can be built very cheaply. However, beyond acting as a component in a relay-attack, a ``leech'' can also be used as a stand-alone RFID skimmer, to surreptitiously read the contents of simple RFID tags. Our goal in this work was to actually build such a skimmer.
1.2 Related work
1.2.1 Attacks on RFID Systems Using the ISO-14443 Standard
The starting point of our work is [KW05]. Their analysis predicts that an RFID tag can be read by the ``leech'' from a range of tens of centimeters, much further than the nominal ISO-14443 range of 5-10 cm. They also claimed that the ``ghost'' device can communicate with the reader from distance of tens of meters. [KW05] presented several variants of possible relay-attack implementations, with different costs and required personnel skills. In this work we validate their claims about the practically of the leech device.Another part of the relay attack against ISO 14443A RFID systems was implemented by Hancke [Han05]: He implemented the fast digital communication between the leech and the ghost (see Figure 1), while using standard (nominal range) devices for the leech and ghost themselves. His system used cheap radios, and achieved a range of 50 meters between the reader+ghost and the leech+tag. His work demonstrates that the range between the victim tag and the reader is limited only by the technology used for leech-ghost communication. To counter the relay attack, [HK05] have designed a distance-bounding protocol, which requires ultra-wide-band communication.
In a widely reported work, Finke and Kelter [FK05]) managed to eavesdrop on the communication between an ISO-14443 RFID reader and a tag. They attached the tag directly to a reader (at zero distance), and showed that the combined communication between the reader and tag can be read from 1-2 meters by large loop antenna located on the same plane of the reader and the tag. Note that this is quite different from the challenges facing a skimmer: (a) The skimmer must be close enough to the tag, and produce a strong enough magnetic field, to power the tag (i.e., the tag must be within ``activation range''); (b) A skimmer cannot rely on a legitimate reader's strong signal being modulated by the tag. Nevertheless, [FK05] shows that the eavesdropping range on RFID communication is a much greater than skimming range--and we show that skimming range is much greater than the nominal read range.
1.2.2 Attacks on RFID Systems Using Other Standards
There are many RFID systems that do not use the ISO-14443 standard. Typically, such systems are designed for larger read-ranges, but provide much more limited capabilities than ISO-14443: they are unable to power a programmable smartcard processor, and usually only contain fixed logic circuitry or even just a short piece of data, much like a magnetic-stripe card. Over the last 2 years, several attacks have been reported against some of these systems.
In a very widely reported event [Kre05,Sch05], a group from Flexilis claimed to set new world record of passively reading an RFID tag from 69 feet at DefCon'05. However, the RFID technology used for this experiment was not ISO-14443, but a UHF-based technology in the frequency range of 800 MHz to 2.5 GHz which is designed for a much larger read range.
A German hacker ([Hes04]) used a simple PDA, equipped with an RFID read/write device, and changed product prices in a grocery shop using a software he wrote. He managed to reduce the Shampoo price from $7 to $3 and go through the cashier without incident. Supermarket checkout trials held by NCR corporation showed that some clients standing at the cashier paid for groceries held by clients standing behind them in the queue [Whi05].
A research team in Johns Hopkins University ([BGS+05]) managed to build a system that sniffs information from RFID-based car keys and immobilizers, and were able to purchase gasoline without the owners consent.
A research group in MIT ([Lin05]) designed and implemented an RFID field probe that can sense RFID magnetic fields from up to 4 meters. However, it is designed to sense magnetic fields of frequencies between 900 to 950 MHz, which are very different from the 13.56 MHz of the ISO 14443 standard.
1.2.3 RFID Systems and Protocols in General
A broad overview of RFID technology can be found in T.A.Scharfeld's thesis [Sch01]. This thesis analyzes RFID theory, standards, regulations, environment influence, and implementation issues.Free attack/analysis tools that detect RFID cards and show their meta information are available from the RFDump web site [GW04]. These tools are able to display and modify the card data, such as the card ID, card type, manufacturer etc.
Juels, Rivest and Szydlo [JRS03] propose a blocking tag approach that prevents the reader from connecting with the RFID tag. Their method can also be used as malicious tool: In order to disrupt the Reader-to-Tag communication, their blocker tag actually performs a denial-of-service attack against the RFID reader protocol by using the ``Tree-Walking Singulation Algorithm'' in the anti-collision mechanism. Juels and Brainard [JB04] propose a variant on the blocker concept which involves software modification to achieve a soft blocking tag.
[Wei03] and [SWE02] offer a ``Hash-Lock'' approach to low cost RFID devices which use a ``lock/unlock'' mechanism to protect against retrieving the RFID ID number. In the simplest scenario, when the tag is locked it is given a value (or meta-ID) y, and it is only unlocked by presentation of a key value x such that y = h(x) for a standard one-way hash function h.
[RCT05] describe a portable device, called an RFID Guardian, that is supposed to cover a whole individual's surrounding, to communicate with the various tags in the person's possession, and protect the person from potentially hostile RFID fields. The RFID Guardian is supposed to be able to cover a range of 1-2 meters, however, the authors do not describe the RFID Guardian implementation, and it is unclear how it overcomes the physical limitations of the claimed range.
1.3 Contribution
In this study we show that the modeling predictions of [KW05] are
quite accurate. We managed to build a portable, extended-range RFID
skimmer, using only electronics hobbyist supplies and tools. Our
skimmer is able to read ISO-14443 tags from a distance of
Beyond validating the theoretical modeling, we believe that our design, implementation and tuning processes are of independent interest: Most circuit designs and application notes are written for well equipped RF labs, and we needed to modify them or design our own to meet our ridiculously low budget. In particular, our experience shows that the standard RFID tuning process, described in ISO 10373-6 ([ISO01], is inappropriate for hobbyist workshops, and may be missing some key details that are necessary to make it work. Instead, we describe several tuning processes that do work reliably, even in low-budget environments.
We conclude that (a) ISO-14443 RFID tags can be skimmed from a distance that does not require the attacker to touch the victim; (b) Simple RFID tags, that respond to any reader, are immediately vulnerable to skimming; and (c) We are about half-way toward a full-blown implementation of the relay-attack predicted by [KW05].
Organization: Section 2 describes our skimmer system's design. Section 3 describes our construction techniques. Section 4 details the tuning methods we experimented with. Section 5 describes the skimmer's actual performance, and we conclude with Section 6. Additional details can be found in an appendix.
2 System Design
RFID systems that are based on the ISO-14443 standard
operate with a 13.56 MHz center frequency, which
mandates RF design methods. The system units should be matched for
maximal power transfer and efficiency, and the whole system
should have an excellent noise figure to
improve the receiving and discrimination circuits sensitivity,
which in turn allows a large read range.
2.1 Design Paradigms
Our assumption is that we are constructing an ad-hoc system for attack purposes, and mass production is not involved. Therefore modular design and perfect implementation are not the main design goals. Instead, we focused on quick, simple, and cheap methods. There are two design paradigms that can be followed; the ``normal'' paradigm is to design all the system sub-units to have a uniform 50The advantages of using standard design include the variety of ready-to-use designs, applications notes, and test equipment. The resulting system is scalable, versatile, and modular. However, the need for accurate design, dealing with accurate filters and semiconductor's min-max parameters and ratings, stretches the design and implementation time, and may cause long and tedious system testing and tuning.
In contrast, designing a proprietary, non-standard interface systems has some practical advantages. First, accuracy is no longer mandatory. Second, the system can work in its natural output and input characteristics without the need to adjust its interfaces to standard characteristics, that might need extra matching networks and components. In particular, some amplifier designs have an output impedance that differs from 50
Since our goal was to emulate a hacker, we chose to follow the proprietary design paradigm. We used 50
2.2 System Units
The skimmer is comprised of 5 basic units (see Figure
2): A reader, a power amplifier, a receive
buffer, an antenna and a power supply. The RFID reader generates all
the necessary RF signals according to the ISO 14443 type A protocol.
These signals are amplified by the power amplifier to generate the
RF power which is radiated through the loop antenna. The loop
antenna performs the interaction with the ISO 14443 RFID tag, and
senses the load modulation signals. These signals are buffered by
the Load Modulation Receive Buffer and fed back to the reader
detection input. The Reader communicates with a host system via an
RS232 serial interface. Typically, the host is a computer, however,
it can also be a small micro-controller based card, with some
non-volatile memory that collects and stores skimmed data.
Our main objective was to increase the output power and antenna size
as these two factors directly influence the reading range.
2.3 The RFID Reader
The RFID reader module we used was the Texas Instrument (TI) S4100 Multi-Function reader module, [TI03]. The module can be purchased alone for around $60, and the TI web site ([TI05]) contains sufficient documentation for designing and programming this module. The S4100 module has a built in RF power amplifier that can drive approximately 200 mW into a small antenna. The TI module supports several RFID standards. We focused on the ISO 14443 Type A standard, that is used in contactless smartcards and E-passports. In addition to the basic S4100 module, we purchased the RX-MFR-RLNK-00 Texas Instrument Multi-Function Reader evaluation kit. The evaluation kit costs $650 and contains a complete ready-to-use reader, which is built around the S4100 module. The kit includes a small built-in 8.5 cm loop antenna and is assembled in a plastic box. It is supplied with basic demo software, various tags for its supported protocols, documentation and references. The kit has an RS232 serial port for interfacing a host computer. We measured a reading range of 6.5 cm using its built in antenna.Although we could have used the (dismantled) evaluation kit's main board for our experimentation, we chose to build our own base board to demonstrate that buying the evaluation kit is not required. We followed the Interface Circuitry design suggested by TI ([TI03]), but omitted the Low Frequency LED driver. We could have omitted the RS232 level shifters and use TTL levels for the serial port communication, however, the skimmer is supposed to work near the antenna, and to be exposed to strong and noisy electro-magnetic fields, therefore we included common RS232 level shifters in our base board design. This design requires a 5 volts power supply. See Section 2.7 for power supply design and description.
2.4 Antennas
A necessary condition for an increased range is a larger antenna. Theoretical analysis ([Lee03]) shows that for a desired range, r, the optimal antenna diameter isFor our larger, high power antenna, we constructed a 39 cm copper tube loop antenna. The basic design for the loop antenna's matching network was taken from the PCB antenna (Figure 3) , subject to minor changes: Specifically, the resonance parallel capacitors C33 and C34 that were merged into one capacitor of 82pF, since the calculated antenna's inductance was around 1
2.5 Power Amplifier
We based our power amplifier on [Mel04], and modified
it to suit our unit's interface. The scheme of the power amplifier we
designed appears
in Figure 4. We interfaced the power amplifier
directly to the TI module's output stage embedded in the skimmer base
board. However, we did not match impedances between the two since
we did not have to transfer power to the power amplifier, but only
drive its input for biasing the power FET by a sufficient voltage
swing.
2.6 The Load Modulation Receive Buffer
The TI S4100 module is designed around the S6700 Multi-Protocol
Transceiver IC, an integrated HF reader system that contains all the
high frequency circuitry comprising an Analog Front End (AFE) that
decodes the ISO standards protocols. The S6700 has a Receiver input,
which is directly connected to the reader's antenna.
This receiver input is unable to handle the voltage levels that are
developed on our large loop antenna: During the system development
process we measured 184 volts over the antenna with a supply voltage
of 17.1 volts. In order to keep the reader from potential damage,
and still deliver the load modulation signals to the reader's
receiver input, we had to attenuate the antenna signals before
feeding them back to the TI module. A simple resistor attenuation
network is not suitable since it dramatically influences the
antenna's resonance circuit quality factor, Q. Therefore, we chose
to use an attenuating buffer (See Figure 5). The
buffer was designed using a high impedance RF FET (T2 in Figure
5), in order to keep the antenna's quality factor as
designed. The buffer was attached to the antenna and to the TI
module via a direct coupling connection, in order to reduce the
signal phase shifting to minimum. The C21 variable capacitor is used
to compensate for the parasitic capacitance introduced by the T2
FET.
2.7 The Power Supply
In order to drive the large loop antenna, we needed to provide a
power supply.
For lab work, we used a stabilized external power supply. Note that
the base board that embeds the TI module contains a voltage
regulator, therefore the external power supply unit does not have to
be regulated. Nevertheless, we used a regulated power supply to
reduce its noise figure. Figure 6 shows the
regulation and filtering circuity which we placed on the base board
and on the power amplifier board.
The role of L52 in Figure 6 is to maintain clean and low ripple levels on the DC supply in order to keep a low noise figure of the DC supply voltage. Since the DC supply voltage reaches all the internal chips circuitry, having clean DC voltage to the internal load modulation signals detection circuitry can improve detection range.
To demonstrate the skimmer's mobility, we also operated it using a Non-Spillable 7 AH Zinc-Lead rechargeable battery used in home security systems. It has a 12 volts nominal voltage level, is very common and can be purchased in any home security system store. An added bonus of using a non-switched DC power supply is that it eliminates any switching noise.
3 System Building
3.1 Printing a PCB Antenna
Our first choice was to build a home made 10x15 cm PCB RFID antenna which is fully specified in the TI antenna cookbook. To demonstrate the low-tech requirements, we manufactured this antenna in our hobby workshop. Appendix A describes the PCB printing process.3.2 Building a Copper Tube Loop Antenna
The TI cookbook describes a design for a square 40x40 cm copper-tube antenna, which seemed appropriate. However, we chose not to construct it precisely, since cheap copper tube (for cooking gas) is sold packed in circular coils, and constructing an antenna with a square or rectangle shape requires straightening the tube, and requires additional 90 degrees matching adapters, which increase the antenna's cost. Instead, we designed our own circular antenna, which has similar characteristics to the TI cookbook antenna. We built the loop antenna from 5/16 inch cooking gas copper tube. The tube is tied to a solid non flexible wooden tablet, in order to maintain its shape and to avoid inductance changes under mechanical deformation forces.The loop antenna construction process was basically mechanical handcraft work, requiring no special equipment beyond basic amateur's electrical tools. Note that copper tube must be soldered using at least a 100-watts blow torch. Figure 7 shows the finished copper tube antenna and the PCB antenna.
3.3 Building the RFID Base Board
According to the interfacing information we found in the S4100 module datasheet, we designed a small PCB base board, having the S4100 module as a Piggy Back. We manufactured the RFID base board PCB using a different method than we used to make the PCB antenna. For this board, we used a Decon DALO 33 Blue PC Etch protected ink pen to draw the leads on the Glass-Epoxy tablet. This technique allowed us to print the PCB during any time of day, without the need to wait for the sun. See Figure 8 for a picture of the base board.3.4 Building the Power Amplifier
As we noted in Section 2.5, the power amplifier design is based on a Melexis application note ([Mel04]), recall Figure 4. We used the output stage of the TI S4100 reader module in the base board to drive the power amplifier input. We did not invest any effort in impedance matching since the power amplifier input is voltage driven. We manufactured the PCB for the power amplifier using the same technique as used for the base board, and with the same low cost DC ripple filter (recall Figure 6) to maintain a low noise figure. Beyond the Melexis design, empirical results led us to connect a filter comprised of R2 and C4 at the output (See Figure 4). This filter reduces the Q of the output impedance matching filter, enabling fine tuning of the output signal phase. We discovered that the filter increased the read range significantly.The output voltage amplitude of the power amplifier varies depending on the power supply voltage. For instance, with a 17.1 volts power supply we measured over 180 volts on the resonance circuit and the antenna. Therefore, ideally, high voltage rating capacitors, and high current rating inductors should be used. We used regular, but easy to obtain, passive components, and managed to burn quite a few during our experimentation.
3.5 Building the Load Modulation Receive Path Buffer
As we mentioned before, the high voltage swing on an antenna driven
by the power amplifier must be attenuated in order to supply the
correct samples of the RF received signal back to receive input of
the S4100 module. Therefore, we needed to build the buffer described
in Section 2.6. We placed the buffer's circuitry on
the same PCB that housed the power amplifier - see Figure
8.
One challenge we had to deal with is that the TI S4100 module is
designed to work with a low power antenna, and includes an
attenuation resistor that is suitable for such an antenna. In order
to provide our (attenuated) signals to the S4100, we had to solder
the buffer's output directly into the S4100 module, bypassing the
original attenuation resistor. Figure 9 shows the
bypass.
4 System Tuning
A crucial implementation phase is system tuning and adjustment.
Specifically, we have to tune the various resonance circuits and
matching networks for maximal power transfer. The only test
equipment we used throughout the entire project was cheap 60 MHz
oscilloscope, that any electronic hobbyist has in his workshop. Note
that while resonance frequency can be tuned using an oscilloscope,
matching the antenna to the amplifier requires a different procedure
since both a magnitude and a phase must be matched.
4.1 Standard Tuning Methods
We say that a tuning method is ``standard'' if it requires a 50Another tuning method is to measure the Voltage Standing Wave Ratio (VSWR), and to adjust the antenna's impedance to be best matched to the driving amplifier output stage by tuning the returned power to the desired value ([Poz05]). This method requires a VSWR meter, which costs several hundred US$: still beyond a typical hobbyist budget. A cheap way to measure the VSWR (without a VSWR meter) is to use directional couplers, that cost between $20-$70, but their input and output impedance is 50
Finally, one can tune the system using an RF watt-meter, or an RF power meter. These instruments sense the RF power and translate the sensor's measurement to a standard scale. The sensor can be based on a diode, or on a bolometer: an RF power sensor whose operation is based on sensing purely resistive element radiation. This method is a second-order-effect tuning since it measures the antenna power reception rather than the actual direct amplifier to antenna matching. This kind of equipment costs between $300 (used) to $600 for a simple watt-meter, including the sensor, to about $3000 for an RF power meter that also features a VSWR meter and various other RF measurement capabilities.
4.1.1 The ISO 10373 Tuning Method
Since tuning the RFID receiver is a critical part of building such a device, Annex B of the ISO 10373-6 standard ([ISO01]) suggests a tuning process. This process seemed attractive since it only calls for low-cost components and uses basic oscilloscope capabilities. Therefore, despite the fact that ISO 10373 is a standard (504.1.2 Problems with ISO 10373
Despite its apparent simplicity, in practice we discovered that the ISO 10373-6 tuning process has a few problems. The first thing to note is that this tuning method requires a 13.56 MHz signal source, with a 50Unfortunately, in all possible settings of the antenna's matching circuitry, we did not manage to get the expected Lissajous figures. In some settings we got wavy figures implying a non linear circuit working point. In other settings we did not get the figures centered around the desired 45 degrees slope. Worst of all, we found no correlation between more closed Lissajous figures and longer read ranges (which we obtained using the methods of sections 4.2 and 4.3.
To our frustration, we found that ISO 10373-6 does not specify the exact oscilloscope Volt per Division setting. This level of detail matters since we are dealing with very fine tuning, and human eye, oscilloscope line thickness and human judgment in conjunction with parallax error, can lead to errors. We speculate that if major RF labs indeed use this standard for tuning, they probably have some additional ``secret sauce'' that fills in the missing details.
One possible reason for our difficulties may be that we used the TI module as a signal source. This improvisation may have inserted some undesired harmonics due to the sidebands in the downlink signal spectrum, interfering with the tuning process. Since the methods described in Section 4.3 were effective, we did not pursue this further.
4.2 Non-Standard Tuning Methods
Instead of the standard 50 The other non-standard method is a trial-and-error iterative process of reading an RFID tag at increasing distances, while tuning the matching circuitry, until a maximal range is reached.
4.3 Tuning Methods that Worked
The antenna has two tuning steps. The first is tuning the resonance
frequency by trimming capacitor C35 in Figure 3.
The second step is tuning the series capacitor C32 in Figure
3 to achieve maximal power transfer to the antenna.
For tuning the resonance circuit we used the power amplifier's
output signal, driven by the reader base board to tune center
resonance frequency.
Then, for tuning the entire system, we used the iterations method
described earlier. For this we used a Philips Mifare Standard IC tag.
Initially, we located the tag at the basic range according to the RFID
standard, and tuned the series antenna network capacitor C32 to some
initial tag read. When an initial reading is observed, we know that
the final position of C32 is near the position of the initial readout.
We gradually increase the power supply, and each time adjust the
various capacitors to get a stable reading range, while increasing the
distance between the tag and the antenna. To hold the tag at a fixed
distance we used non-ferromagnetic objects: most of the time we used a
stack of disposable plastic cups, and for fine range measurements we
used a small supply of 1-2mm thick beer coasters, see Figure
12. We stopped at a 19 volts power supply since the
maximum semiconductor ratings were reached. Surprisingly, the
variable capacitors survived the high swing voltage, which was more
than 180 Volts.
The Unseen Side Of Things, And It Will Change The Way You See The World
This Is A Photo NASA Took Of A Space Shuttle Leaving Our Atmosphere

#2 The Inside Of This Guitar Looks Like An Apartment I Can't Afford

#3 This Is How Brick Streets Are Laid In The Netherlands

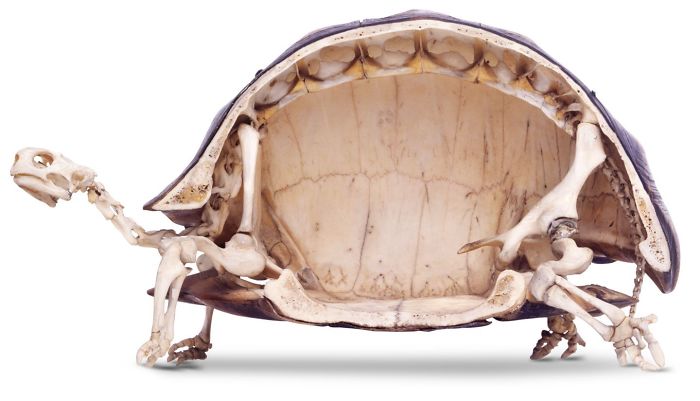
#4 Tortoises Have The Weirdest Looking Skeletons
#5 This Is What The Underside Of A Lilly Pad Looks Like

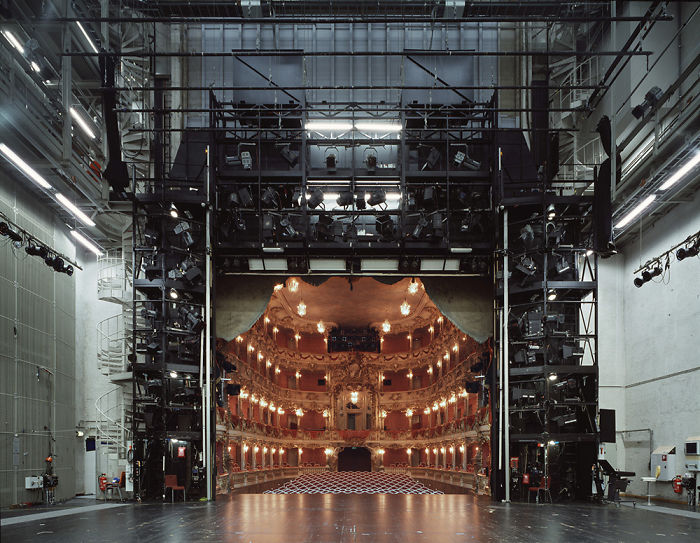
#6 Looking Into A Theatre From Behind The Stage
#7 The Blood Vessels Of A Hand

#8 What A Modern Battleship Looks Like With No Water Around It

Subscribe to:
Comments (Atom)






